What is file encoding malware
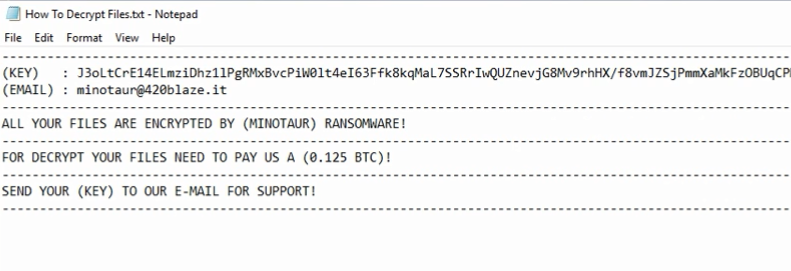
Minotaur ransomware will encrypt your files, since that is the primary intent of ransomware. It really depends on which ransomware is to blame, but you may not be able to access your data again. In addition, infection can happen very quickly, which is one of the reasons why data encoding malware is so dangerous. If you have it, you possibly opened a spam email attachment, pressed on a malicious ad or fell for a bogus download. As soon as the ransomware is done encoding your files, a ransom note will be delivered to you, asking for money for a tool that would supposedly decrypt your data. You might be requested to pay $50, or $1000, it all depends on which ransomware you have. If you’re thinking about paying, look into alternatives first. Considering crooks will feel no obligation to help you in file recovery, it is probable they will just take your money. You certainly would not be the only person to be left with locked files after payment. Instead of paying, you should buy backup. We are sure you can find a good option as there are plenty to select from. If backup was made prior to you infecting your computer, file restoration will be achievable after you eliminate Minotaur ransomware. It is critical that you prepare for these types of situations because you’ll probably get infected again. If you wish your computer to be infection-free, you’ll have to learn about malware and how it can enter your machine.
Download Removal Toolto remove Minotaur ransomware
File encoding malicious software distribution methods
Although you could find exceptions, the majority of file encrypting malicious program tend to use the most basic methods of infection, like spam email, corrupted adverts and downloads. It does, however, sometimes use methods that are more sophisticated.
The likely way you got the file encrypting malware is via email attachment, which could have came from an email that initially looks to be completely legitimate. Crooks spreading data encrypting malicious software add an infected file to an email, send it to hundreds of people, who infect their computers as soon as they open the file. Cyber crooks can make those emails quite convincing, normally using topics like money and taxes, which is why it’s not really surprising that those attachments are opened. In addition to errors in grammar, if the sender, who definitely knows your name, uses greetings such as Dear User/Customer/Member and strongly pressures you to open the file attached, it could be a sign that the email isn’t what it appears. If the sender was a company whose services you use, your name would be inserted automatically into the email they send you, and a general greeting wouldn’t be used. You might encounter company names such as Amazon or PayPal used in those emails, as known names would make users trust the email more. Clicking on advertisements hosted on dubious websites and getting files from unreliable sources could also lead to an infection. Compromised websites could host malicious advertisements so stop engaging with them. Avoid unreliable pages for downloading, and stick to valid ones. Sources like advertisements and pop-ups are not good sources, so never download anything from them. Programs usually update themselves, but if manual update was needed, you would get an alert through the application, not the browser.
What happened to your files?
A very big reason on why data encrypting malware are thought to be a highly harmful infection is because it could encrypt your files in a way that makes decryption very unlikely. It can take mere minutes for it to find the files it wants and encrypt them. Strange file extensions will appear added to all affected files, from which you can judge which data encoding malware has infected your device. Your data will be locked using strong encryption algorithms, which may be impossible to break. When the encryption process is finished, a ransom note should appear, and it should explain how you should proceed. It will encourage you to buy a decryptor, but buying it isn’t something we suggest doing. Complying with the demands doesn’t necessarily mean data decryption because hackers could just take your money, leaving your files locked. Additionally, you would be financing the future activities of these crooks. These types of infections are believe to have made $1 billion in 2016, and such a successful business will just attract more and more people. Instead of paying the ransom, we suggest buying backup. If this kind of situation occurred again, you could just get rid of it without worrying about losing your files. If you have decided to ignore the demands, you will have to remove Minotaur ransomware if you know it to still be inside the computer. If you become familiar with how these infections are distributed, you ought to be able to dodge them in the future.
Minotaur ransomware termination
For the process of completely getting rid of the data encrypting malware, you will need to acquire malicious threat removal software, if it is not already present on your computer. Because your computer got infected in the first place, and because you are reading this, you may not be very computer-savvy, which is why it’s not recommended to manually delete Minotaur ransomware. A wiser choice would be employing anti-malware software to do it for you. It shouldn’t have any issues with the process, as those types of tools are developed to eliminate Minotaur ransomware and similar infections. In case there is a problem, or you are not certain about where to begin, you’re welcome to use the below provided guidelines. Sadly, the anti-malware isn’t capable of decrypting your files, it will only erase the threat. In certain cases, however, malware researchers can develop a free decryption utility, so occasionally check.
Download Removal Toolto remove Minotaur ransomware
Learn how to remove Minotaur ransomware from your computer
- Step 1. Remove Minotaur ransomware using Safe Mode with Networking.
- Step 2. Remove Minotaur ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Minotaur ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Minotaur ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Minotaur ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

