Is Petruk ransomware a serious ransomware
Petruk ransomware ransomware may bring about serious damage because it will encrypt files. Due to how ransomware behaves, it is very dangerous to have ransomware on the computer. When the ransomware launches, it locates specific files to encrypt. Most commonly, the targeted files include photos, videos, documents, essentially all files people would be prone to paying money for. The key you need to unlock your files is in the possession of criminals behind this ransomware. A free decryptor might become available at some point if malicious software researchers could crack the ransomware. This is your best option if you don’t have backup.
Download Removal Toolto remove Petruk ransomware
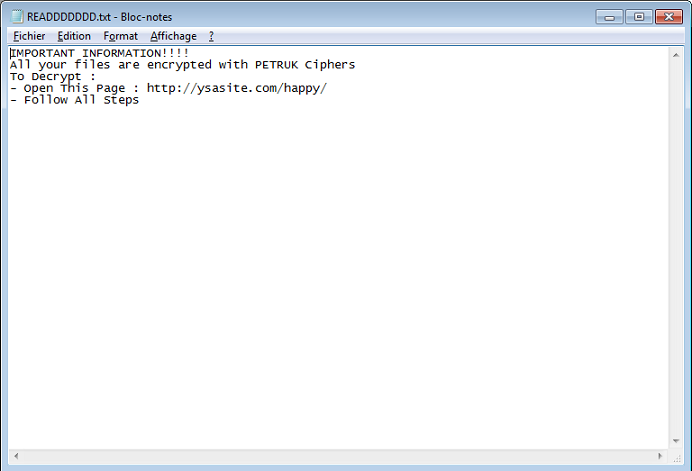
If you are yet to notice it, a ransom note has been placed on your desktop or among encrypted files in folders. You will see a short explanation about what happened to your files in the note, in addition to being offered to buy a decryption tool. While we cannot say what you should do as we are talking about your files but paying for a decryption application is not recommended. It would not shocked us if the hackers just take your money. Additional malware would be developed using that money. Maybe investing into backup would be better. Just remove Petruk ransomware if you do have backup.
If you carry on reading, we’ll discuss how the threat managed to get into your system, but to summarize, you likely encountered it in spam emails and false updates. Such methods are quite often used by cyber crooks as advanced knowledge isn’t needed.
How is ransomware spread
Spam emails and fake updates are generally how users get contaminated with ransomware, despite the fact that other distribution methods also exist. Since malicious spam campaigns are quite typical, you have to familiarize yourself with what dangerous spam look like. When dealing with unknown senders, don’t rush to open the attached file and thoroughly check the email first. It ought to also be said that crooks frequently pretend to be from well-known companies in order to make users feel safe. You might get an email with the sender claiming to be from Amazon, warning you about some type of unusual behavior on your account or a recent purchase. You could make sure the sender is actually who they say they are without difficulty. Just find a list of email addresses used by the company and see if your sender’s is among them. Moreover, use an anti-malware scanner to make sure the file is harmless before opening it.
It is also not impossible that bogus program updates were used for ransomware to enter. High-risk sites are where we believe you encountered the bogus update notifications. Frequently, the false update notifications could appear in banner or ad form. For those familiar with how notifications about updates look, however, this will cause immediate doubt. If you wish to have an infection-free computer, you ought to never download anything from advertisements or other questionable sources. If a program has to be updated, you will be alerted by the program itself or it’ll happen automatically.
What does ransomware do
Your files have been encrypted, as you’ve probably noticed by now. File encrypting likely happened without you knowing, right after the contaminated file was opened. All locked files will have an unusual extension, so you’ll know which files have been affected. If your files have been locked, they’ll not be openable as they were encrypted with a strong encryption algorithm. Information about how to restore your files should be found on the ransom note. The ransom notes generally tend to threaten users with file deletion and encourage victims to pay the ransom. Giving into the requests is not the best idea, even if hackers have the decryption utility. It is not likely that the people responsible for your file encryption will feel obligation to unlock them after you pay. Moreover, if you gave in once, hackers may make you a victim again.
Before you even think about paying, try to remember if you’ve uploaded some of your files anywhere. If you’re out of choices, back up the locked files for safekeeping, it is not impossible that a malicious software researcher will release a free decryption tool and you could be able to recover files. Whichever choice you pick, you will still need to uninstall Petruk ransomware.
Whatever choice you have made, you have to begin backing up your files on a frequent basis. If you don’t take the time to make backups, this situation might happen again. There is a variety of backup options available, some more expensive than others but if you have files that you value it’s worth obtaining one.
How to uninstall Petruk ransomware
Attempting manual removal isn’t a good idea. Allow malware removal program to take care of the ransomware because otherwise, you might end up doing more harm. If malicious software removal program can’t be launched, load your system in Safe Mode. The malicious software removal program should run properly in Safe Mode, so there should be no problems when you erase Petruk ransomware. Keep in mind that anti-malware program can’t help you with files, it will only eliminate ransomware for you.
Download Removal Toolto remove Petruk ransomware
Learn how to remove Petruk ransomware from your computer
- Step 1. Remove Petruk ransomware using Safe Mode with Networking.
- Step 2. Remove Petruk ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Petruk ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Petruk ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Petruk ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

