Is this a serious malware
.Kromber file virus will effect your system very seriously because it will lock your files. Generally, ransomware is classified as a highly dangerous infection because of the consequences it will bring. A file encryption process will be launched soon after the contaminated file is opened. Photos, videos and documents are among the most targeted files due to their value to victims. Files cannot be opened so easily, you will need to decrypt them using a decryption key, which is in the hands of the hackers who encrypted your files in the first place. The good news is that ransomware is every now and then cracked by people specializing in malicious software, and a free decryption application might become available. If backup is not available, waiting for that free decryptor is your only option.
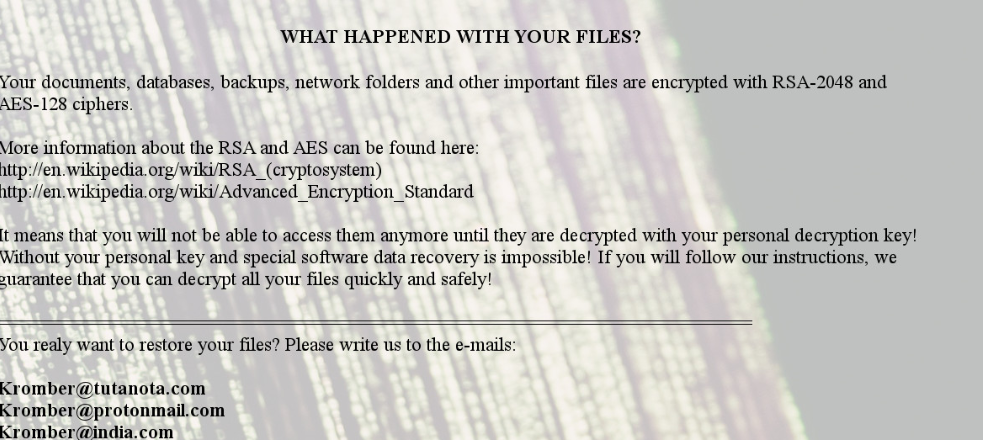
In addition to finding files encrypted, a ransom note will also be placed somewhere on your OS. The hackers behind this ransomware will offer you to buy a decryption application, explaining that using it is the only way to get files back. Our next statement will not surprise you but it’s not advised to engage with crooks. It’s not an impossible for crooks to just take your money without helping you. Your money would go towards developing more malicious software. Seeing as you’re considering paying criminals, perhaps purchasing backup would be a wiser decision. In case you have made copies of your files, just terminate .Kromber file virus.
Download Removal Toolto remove .Kromber file virus
We’ll clarify in more detail how the threat managed to get in, but to summarize, you probably encountered it in spam emails and false updates. These are two of the most frequently used ways of distributing malware.
Ransomware distribution ways
Spam emails and fake updates are probably how you got your computer infected with ransomware, even though there are other distribution ways. Since of how common spam campaigns are, you have to familiarize yourself with what malicious spam look like. If you get an email from an unfamiliar sender, you have to cautiously check the contents before you open the file attached. It is also rather usual for crooks to pretend to be from notable companies, as a familiar name would make people less cautious. For example, they may claim to be Amazon and say that the attached file is a receipt for a recent purchase. If the sender is actually who they say they are, checking that won’t be difficult. Check the sender’s email address, and whether it sees real or not check that it really belongs to the company they claim to be from. Moreover, use a malware scanner to check the file before you open it.
Fake application updates could have also been how you picked up the ransomware. Those types of malicious software update offers may appear when you visit websites with dubious reputation. They also appear in advertisement form and could seem fully valid. Nevertheless, because updates will never be pushed this way, people who know how updates work will not fall for it. If you want to have a malware-free computer, you should never download anything from questionable sources. If you’ve set automatic updates, updates will happen automatically, but if you have to manually update something, you’ll be alerted via the software itself.
How does this malware behave
While you have likely already realized this, but ransomware locked your files. As soon as the contaminated file was opened, the ransomware began its file encryption process, which you might not have necessarily noticed. Affected files will now have a file extension added to them, which will help you quickly see which files have been affected. Because a complex encryption algorithm was used, you won’t be able to open the affected files so easily. A ransom notification will then appear, where hackers will explain that your files have been encrypted, and how to go about recovering them. If it isn’t your first time dealing with ransomware, you will see a certain pattern in ransom notes, crooks will intimidate you to think your only option is to pay and then threaten to remove your files if you do not give in. Despite the fact that hackers have the only decryptor for your files, paying the ransom isn’t recommended. Realistically, how likely is it that cyber criminals, who encrypted your files in the first place, will feel obligated to recover your files, even after you pay. Furthermore, if you paid once, cyber crooks could try targeting you again.
You might have stored some of your files somewhere, so try to recall before you even consider paying. Some time in the future, malware specialists may make a decryption tool so backup your encrypted files. Whichever choice you opt for, it is still necessary to erase .Kromber file virus.
Having copies of your files is rather important, so begin frequently making backups. You might be put into a similar situation again which might result in permanent file loss. There are various backup options available, some more pricey than others but if you have files that you value it’s worth obtaining one.
Ways to remove .Kromber file virus
Attempting manual elimination could result in more harm than good so we do not suggest trying it. Obtain and have anti-malware program to take care of the ransomware because otherwise, you could cause more harm. You might have to load your system in Safe Mode for the malicious software removal program to work. After you launch malicious software removal program in Safe Mode, you should not come across problems when you attempt to delete .Kromber file virus. Terminating the malware won’t help with file recovery, however.
Download Removal Toolto remove .Kromber file virus
Learn how to remove .Kromber file virus from your computer
- Step 1. Remove .Kromber file virus using Safe Mode with Networking.
- Step 2. Remove .Kromber file virus using System Restore
- Step 3. Recover your data
Step 1. Remove .Kromber file virus using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove .Kromber file virus.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove .Kromber file virus using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

