About this threat
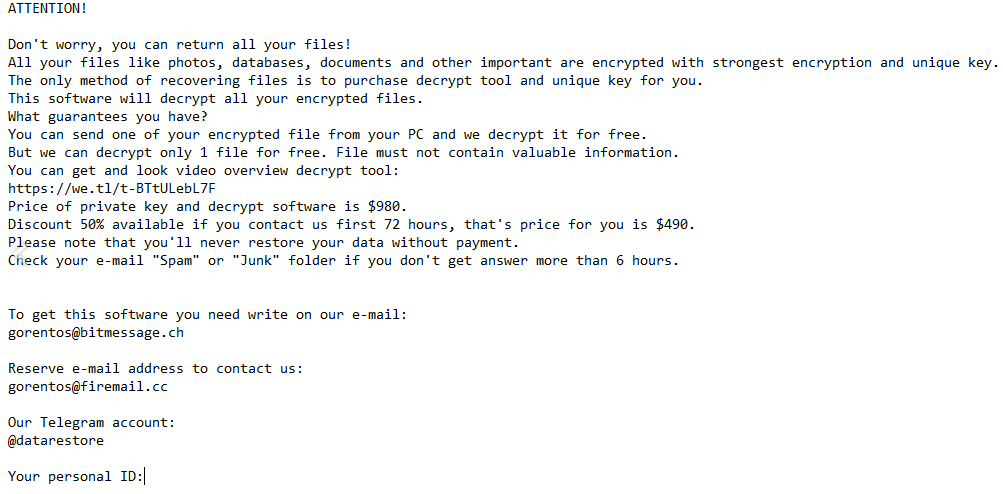
.jdyi files file encrypting malware will encrypt your files and you’ll be unable to open them. Ransomware is the name you ought to be more familiar with in regards to this kind of malicious software. There are a couple of ways the infection may have entered your system, probably either via spam email attachments, infected adverts and downloads. It’ll be explained this further in the proceeding section. A file-encrypting malware infection could lead to very severe outcomes, so it’s essential to know its distribution methods. It may be especially shocking to find your files encrypted if you have never happened upon ransomware before, and you have little idea about what it is. Soon after you see that something is wrong, a ransom message will appear, which will reveal that if you want to get your files back, you have to pay money. Remember who you’re dealing with if you consider giving into the requests, because we doubt crooks will bother sending a decryption program. The cyber crooks will probably just ignore you after you make the payment, and we doubt they’ll help you. This, in addition to that money supporting an industry that does millions of dollars in damages, is why giving into the demands is not recommended. There’s a likelihood that a free decryptor has been made, as people specializing in malware in some cases are able to crack the ransomware. Research free decryptor before you even think about paying. For those careful enough to have backup, simply terminate .jdyi files and then access the backup to restore files.
Download Removal Toolto remove .jdyi files
Ransomware spread methods
There are different ways you could have acquired the file encrypting malware. Ransomware generally sticks to simple methods, but more sophisticated ones are used as well. We’re talking about methods such as sending spam emails or hiding malware as valid downloads, basically things that may be done by low-level crooks. You probably picked up the infection when you opened an infected email attachment. The file contaminated with ransomware is added to a kind of legitimate email, and sent to all potential victims, whose email addresses they store in their database. It is not really that surprising that users open these emails, if it is their first time coming across it. If you see that the sender’s email address is completely random, or if there are a lot of grammar mistakes, those might be signs that it is a malicious email, particularly if it is in your spam folder. It should also be mentioned that hackers use popular company names to not rouse distrust. Our recommendation would be that even if you know who the sender is, the sender’s address should still be checked. If the email doesn’t have your name, that ought to raise suspicion. If you receive an email from a company/organization you’ve dealt with before, instead of Member or User, they’ll include your name. For example, Amazon automatically inserts customer names (or the names users have provided them with) into emails they send, therefore if the sender is actually Amazon, you’ll see your name.
In a nutshell, before you hurry to open files attached to emails, make sure the sender is who they claim they are and you won’t be risking losing your files. And when you’re visiting dubious pages, don’t go around interacting with advertisements. If you’re not careful, ransomware may end up entering your computer. Adverts shouldn’t always be relied on so avoid engaging with them, whatever they could be offering. By downloading from unreliable sources, you might also be endangering your device. If you are downloading via torrents, the least you can do is read the comments before you download something. There are also cases where vulnerabilities in programs might be used for the infection to be able to get in. You need to regularly update your software because of that. You just have to install the updates that software vendors make available for you.
How does ransomware act
When the infected file is opened, the threat will search for certain file types. Files targeted for encryption will be documents, media files (photos, video, music) and everything you hold important. The file-encrypting malware will use a strong encryption algorithm for file encryption once they have been found. The file extension attached will help you find out with files have been affected. The ransom message, which you should notice soon after the ransomware is finished locking your files, will then ask payment from you to get a decryptor. How much you are demanded to pay varies from ransomware to ransomware, the amount might be $50 or it may be a $1000. While we’ve already stated why we do not suggest paying, in the end, this is your choice. Before you consider paying, you need to look into all other ways to recover data. It’s possible that researchers specializing in malware were able to crack the ransomware and release a free decryption program. You could also just not recall backing up your files, at least some of them. Your device stores copies of your files, known as Shadow copies, and if the ransomware didn’t erase them, you can recover them via Shadow Explorer. We hope you have gotten backup and will start backing up your files, so that this situation doesn’t happen again. If backup is an option, you may proceed to recover files from there after you fully delete .jdyi files.
How to eliminate .jdyi files
Manually uninstalling the infection is possible, but not something that we advise. You may bring about irreversible harm to your machine, if errors are made. Our recommendation would be to obtain a malware removal utility instead. Because those tools are developed to remove .jdyi files and other infections, you should not encounter any problems. However, do keep in mind that a malware elimination software will not help with file recovery, it’s just not able to do that. This means you will have to research how to restore data yourself.
Download Removal Toolto remove .jdyi files
Learn how to remove .jdyi files from your computer
- Step 1. Remove .jdyi files using Safe Mode with Networking.
- Step 2. Remove .jdyi files using System Restore
- Step 3. Recover your data
Step 1. Remove .jdyi files using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove .jdyi files.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove .jdyi files using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

