What can be said about this .Redmat file virus virus
.Redmat file virus is a file-encrypting malware, known as ransomware in short. If ransomware was unfamiliar to you until now, you are in for a surprise. Powerful encryption algorithms are used by ransomware for data encryption, and once they’re locked, you won’t be able to open them. This is why file encrypting malicious software is classified as harmful malicious software, seeing as infection may lead to your files being encrypted permanently. Criminals will give you the option of decrypting files by paying the ransom, but that is not a encouraged option for a couple of reasons. Paying will not necessarily ensure that you will get your data back, so there is a possibility that you might just be spending your money on nothing. Consider what’s preventing crooks from just taking your money. The cyber crooks’ future activities would also be financed by that money. Do you actually want to support an industry that costs billions of dollars to businesses in damage. And the more people give them money, the more of a profitable business ransomware becomes, and that attracts many people to the industry. Buying backup with the requested money would be better because if you are ever put in this type of situation again, you could just recover files from backup and not worry about losing them. You could then just erase .Redmat file virus and recover data. If you didn’t know what ransomware is, you may not know how it managed to infect your system, in which case carefully read the below paragraph.
Download Removal Toolto remove .Redmat file virus
How does ransomware spread
A file encrypting malware could infect pretty easily, usually using such basic methods as attaching infected files to emails, using exploit kits and hosting infected files on dubious download platforms. Because users are rather careless when dealing with emails and downloading files, there is often no need for ransomware spreaders to use more elaborate methods. That’s not to say that spreaders do not use more sophisticated ways at all, however. Crooks don’t have to do much, just write a generic email that appears quite convincing, attach the contaminated file to the email and send it to hundreds of people, who may think the sender is someone trustworthy. Because of the topic sensitivity, users are more likely to open money-related emails, thus those types of topics are often used. Oftentimes, criminals pretend to be from Amazon, with the email notifying you that suspicious activity was noted in your account or some type of purchase was made. You need to look out for certain signs when opening emails if you want an infection-free computer. If the sender isn’t known to you, before you open any of the attached files they have sent you, look into them. Do no rush to open the attachment just because the sender sounds real, you first need to double-check if the email address matches the sender’s real email. The emails can be full of grammar mistakes, which tend to be quite easy to see. Another typical characteristic is your name not used in the greeting, if a legitimate company/sender were to email you, they would definitely use your name instead of a general greeting, like Customer or Member. Vulnerabilities on your computer Out-of-date programs might also be used to infect. A program has certain weak spots that can be exploited for malware to enter a system, but they’re fixed by authors soon after they’re discovered. As WannaCry has proven, however, not everyone rushes to install those updates. We suggest that you update your programs, whenever a patch becomes available. Updates can install automatically, if you find those alerts annoying.
How does it act
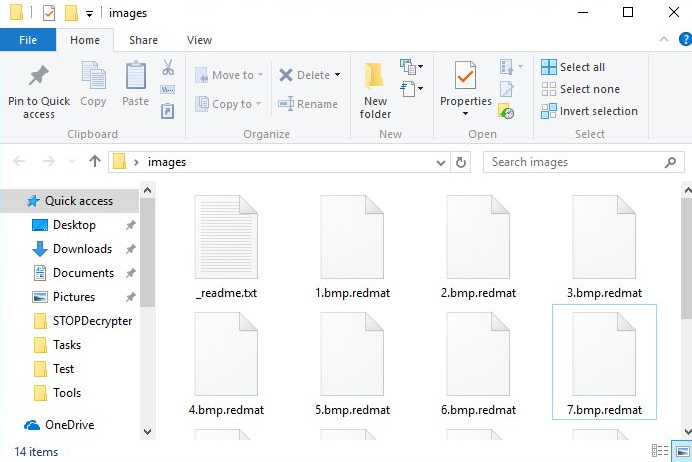
Soon after the file encoding malware gets into your computer, it will look for specific file types and once they’ve been identified, it’ll encrypt them. You might not see at first but when your files cannot be opened, you’ll see that something is going on. Check your files for weird extensions added, they they’ll help recognize the ransomware. Unfortunately, it might not be possible to restore data if a strong encryption algorithm was implemented. You will notice a ransom note placed in the folders containing your data or it will show up in your desktop, and it should explain that your files have been locked and how to proceed. According to the crooks, the only way to restore your files would be with their decryptor, which will not be free. A clear price ought to be displayed in the note but if it’s not, you’ll have to email criminals via their given address. For already discussed reasons, paying the crooks isn’t the suggested choice. Only consider paying as a last resort. Try to recall whether you’ve recently backed up your data somewhere but forgotten. Or maybe a free decryptor is an option. We should say that in certain cases malicious software researchers are capable of decrypting a file encrypting malicious program, which means you could get a decryption program for free. Before you decide to pay, consider that option. A wiser purchase would be backup. If you created backup before the infection took place, you might perform file recovery after you remove .Redmat file virus virus. Now that you are aware of how dangerous file encrypting malicious program can be, try to dodge it as much as possible. Ensure you install up update whenever an update is released, you do not open random files attached to emails, and you only trust legitimate sources with your downloads.
.Redmat file virus removal
In order to get rid of the file encoding malware if it’s still present on the system, a malware removal program will be needed to have. When attempting to manually fix .Redmat file virus virus you may cause additional damage if you’re not cautious or knowledgeable when it comes to computers. Therefore, choosing the automatic method would be a wiser idea. A malware removal software is created for the purpose of taking care of these kinds of infections, it might even prevent an infection from entering in the first place. So research what fits your needs, install it, scan the computer and once the ransomware is found, eliminate it. Do not expect the anti-malware utility to help you in file recovery, because it won’t be able to do that. If the file encoding malicious program has been terminated fully, recover files from backup, and if you do not have it, start using it.
Download Removal Toolto remove .Redmat file virus
Learn how to remove .Redmat file virus from your computer
- Step 1. Remove .Redmat file virus using Safe Mode with Networking.
- Step 2. Remove .Redmat file virus using System Restore
- Step 3. Recover your data
Step 1. Remove .Redmat file virus using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove .Redmat file virus.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove .Redmat file virus using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

