About ransomware
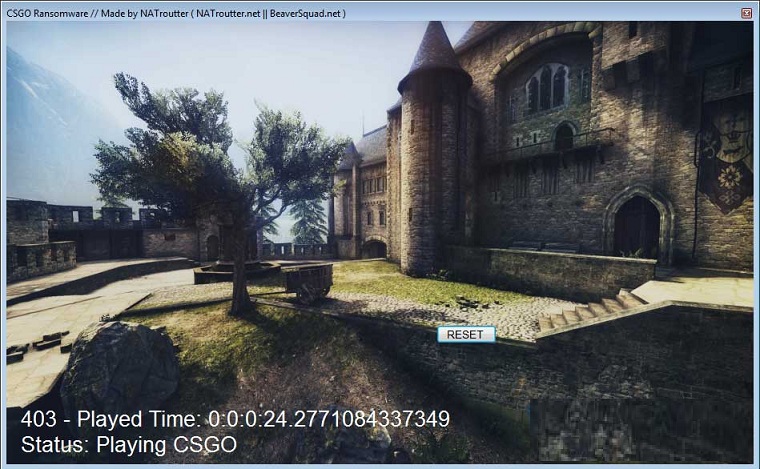
Csgo ransomware is a file-encrypting malware, but the categorization you probably have heard before is ransomware. You may not necessarily have heard of or ran into it before, and it could be especially shocking to find out what it does. Your data might have been encrypted using powerful encryption algorithms, making you not able to access them anymore. Because file encrypting malware could mean permanent data loss, this kind of infection is highly dangerous to have. You’ll be given the option of recovering files by paying the ransom, but that option is not encouraged for a couple of reasons. Paying doesn’t automatically result in decrypted data, so there is a possibility that you may just be wasting your money. Consider what is stopping crooks from just taking your money. In addition, by paying you’d be financing the crooks’ future projects. Do you really want to be a supporter of criminal activity that does billions worth of damage. And the more people give them money, the more profitable ransomware gets, and that attracts many people to the industry. Consider buying backup with that money instead because you might be put in a situation where data loss is a risk again. You could then recover files from backup after you delete Csgo ransomware virus or similar infections. If you’re confused about how the threat managed to get into your computer, we’ll discuss the most frequent spread methods in the following paragraph.
Download Removal Toolto remove Csgo ransomware
Ransomware distribution ways
Email attachments, exploit kits and malicious downloads are the most frequent file encrypting malware distribution methods. Quite a big number of ransomware rely on user carelessness when opening email attachments and more sophisticated methods aren’t necessary. It could also possible that a more sophisticated method was used for infection, as some ransomware do use them. Criminals add an infected file to an email, write a plausible text, and falsely claim to be from a real company/organization. You will frequently come across topics about money in those emails, as those kinds of sensitive topics are what users are more prone to falling for. Cyber criminals prefer to pretend to be from Amazon and caution you that strange activity was noted in your account or a purchase was made. You need to look out for certain signs when opening emails if you want to secure your computer. Before opening the attachment, look into the sender of the email. Even if you know the sender, you should not rush, first check the email address to ensure it matches the address you know to belong to that person/company. Those malicious emails are also frequently full of grammar mistakes. You ought to also take note of how the sender addresses you, if it is a sender with whom you’ve had business before, they’ll always greet you by your name, instead of a universal Customer or Member. Weak spots on your system Out-of-date software might also be used to infect. All software have weak spots but when they are found, they’re normally patched by vendors so that malware cannot take advantage of it to enter. Unfortunately, as shown by the WannaCry ransomware, not everyone installs those patches, for one reason or another. We encourage that you install an update whenever it is made available. Regularly being bothered about updates may get bothersome, so you could set them up to install automatically.
What does it do
When your device becomes contaminated, it will scan for specific files types and encrypt them once they’re located. You might not see at first but when you cannot open your files, it will become obvious that something has happened. Files which have been encoded will have a file extension, which can help recognize the ransomware. In a lot of cases, data restoring may not be possible because the encryption algorithms used in encryption could be undecryptable. In case you’re still unsure about what’s going on, the ransom note ought to clear everything up. The decryption software offered won’t be for free, of course. If the price for a decryption program is not specified, you would have to contact the criminals, normally through the address they provide to find out how much and how to pay. Obviously, we don’t suggest you pay, for the reasons already discussed. When any of the other option doesn’t help, only then you ought to think about paying. Try to remember whether you’ve ever made backup, your files may be stored somewhere. You may also be able to find a free decryptor. If the ransomware is decryptable, a malware researcher might be able to release a tool that would unlock Csgo ransomware files for free. Consider that before paying the demanded money even crosses your mind. Using the demanded sum for a reliable backup may do more good. And if backup is available, you may restore files from there after you remove Csgo ransomware virus, if it still remains on your computer. If you wish to secure your device from ransomware in the future, become aware of means it might infect your computer. You essentially have to update your software whenever an update becomes available, only download from secure/legitimate sources and stop randomly opening email attachments.
How to delete Csgo ransomware virus
Obtain an anti-malware program because it will be necessary to get the ransomware off your computer if it is still in your device. To manually fix Csgo ransomware is no simple process and might lead to further damage to your device. Instead, using a malware removal utility would not jeopardize your device further. This program is handy to have on the device because it will not only make sure to fix Csgo ransomware but also stopping one from getting in in the future. Find which anti-malware program is most suitable for you, install it and allow it to execute a scan of your device in order to locate the threat. Sadly, those programs won’t help to recover files. If your computer has been thoroughly cleaned, go unlock Csgo ransomware files from backup.
Download Removal Toolto remove Csgo ransomware
Learn how to remove Csgo ransomware from your computer
- Step 1. Remove Csgo ransomware using Safe Mode with Networking.
- Step 2. Remove Csgo ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Csgo ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Csgo ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Csgo ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

