What is data encoding malicious program
Cossy Ransomware ransomware is a file-encrypting malware infection that will do a lot of damage. It is a very dangerous threat, and it could lead to serious issues, like permanent data loss. Furthermore, contaminating your computer is very easy, which is one of the reasons why ransomware is so dangerous. Spam email attachments, malicious ads and bogus downloads are the most typical reasons why file encrypting malicious software may be able to infect. Once the data encoding malware is finished encoding your files, you’ll get a ransom note, demanding money for a tool that would supposedly decrypt your data. The money you are asked to pay is likely to differ depending on the type of file encrypting malicious software you have, but should range from $50 to possibly thousands of dollars. We do not suggest paying, no matter how small the amount is. Trusting criminals to keep their word and restore your files would be naive, since they might simply take your money. It would not be shocking if you were left with locked files, and you would certainly not be the only one. This type of situation could reoccur, so instead of giving into the requests, consider investing into backup. We are sure you will find an option that suits your needs as there are many to pick from. If backup was made prior to your device becoming contaminated, you will be able to recover files after you eliminate Cossy Ransomware. This isn’t the last time you’ll get contaminated with some kind of malware, so you ought to be ready. If you wish to remain safe, you have to become familiar with likely threats and how to protect your system from them.
Download Removal Toolto remove Cossy Ransomware
How does data encrypting malicious software spread
does not use complex ways to spread and tends to stick to sending out emails with infected attachments, compromised ads and corrupting downloads. More elaborate methods could be used too, however.
You likely obtained the infection via email attachment, which might have came from an email that seems completely legitimate in the beginning. You open the email, download and open the attachment and the ransomware is now able to begin encoding your data. It’s not odd for those emails to cover money related topics, which is the topic users are likely to think is important, thus would open such an email without hesitation. The use of basic greetings (Dear Customer/Member), prompts to open the attachment, and many grammatical errors are what you need to be caution of when dealing with emails that contain files. To clarify, if someone important would send you an attachment, they would would know your name and would not use general greetings, and it wouldn’t end up in spam. You will also notice that criminals like to use big names like Amazon, PayPal, etc so that people become more trusting. permitted the threat to enter your computer. Compromised pages could host infected advertisements so stop pressing on them. And when it comes to downloads, only trust legitimate websites. Never get anything, whether it is programs or updates, from sources like ads or pop-ups. If an application needed to update itself, it would do it itself or notify you, but never via browser.
What does it do?
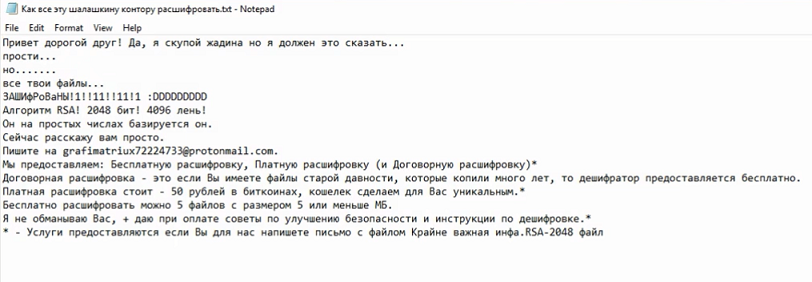
Malware specialists are always warning about the dangers of ransomware, most importantly, its ability to permanently encode files. It has a list of target files, and their encryption will take a very short time. Strange file extensions will appear attached to all affected files, from which you may judge which data encrypting malware you are dealing with. A data encoding malicious software tends to use strong encryption algorithms to encrypt files. If you do not understand what is going on, a dropped ransom note should explain everything. The ransom note will demand that you buy a decryptor, but think about all you choices before you opt to do as cyber crooks ask. Remember that you’re dealing with crooks, and they could simply take your money not giving you a decryptor in return. The ransom money would also likely go towards financing future ransomware or other malware projects. And, more and more people will become interested in the business which is thought to have made $1 billion in 2016. Investing into backup instead of giving into the demands would be a much wiser idea. And your data would not be at risk if this kind of situation occurred again. Just pay no mind to the demands and remove Cossy Ransomware. And attempt to avoid such infections in the future.
Ways to delete Cossy Ransomware
In order to make sure the infection is fully gone, you will need to acquire malicious program removal software. If you try to manually delete Cossy Ransomware, you may accidentally end up harming your computer, so we do not encourage proceeding by yourself. It would be a wiser idea to use anti-malware software because you would not be risking harming your system. Malicious threat removal programs are developed to erase Cossy Ransomware and all other similar infections, so issues should not occur. So that you are not left on your own, instructions below this article have been placed to help you. Sadly, the anti-malware isn’t capable of decrypting your files, it will only erase the threat. But, you ought to also know that some ransomware is decryptable, and malware specialists could release free decryption utilities.
Download Removal Toolto remove Cossy Ransomware
Learn how to remove Cossy Ransomware from your computer
- Step 1. Remove Cossy Ransomware using Safe Mode with Networking.
- Step 2. Remove Cossy Ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Cossy Ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Cossy Ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Cossy Ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

