What is file-encoding malware
Test ransomware can be the ransomware to blame for your file encryption. Normally, ransomware uses spam emails and malicious downloads to infect users, which is how it could have infected your machine. File-encrypting malicious software is believed to be a very harmful malware since it encrypts data, and requests for money in exchange for getting them back. If if you regularly backup your files, or if damaging software specialists release a free decryptor, file-recovery should not be complex. Other than that, data recovery could be impossible. Ransom payment does not mean you will recover your files so take that into consideration if you decide to pay. There are plenty of of cases when file-encrypting malicious software creators just take the money and leave files encrypted. Since payment is not a trustworthy file recovery choice, you ought to just terminate Test ransomware.
Download Removal Toolto remove Test ransomware
How does ransomware act
Be more careful about opening files attached to emails as that is the possible way you could have acquired the threat. Adding a contaminated file to an email and sending it to many users is all that has to be done by malicious program makers so as to infect. The ransomware will be able to download onto the system the moment the email attachment is opened. Reckless or less informed users could be putting their machines in jeopardy by opening every single email attachment that reach their inbox. You must learn the signs of a malicious email, otherwise you will end up with a malicious one someday. No matter how legitimate the email may appear, be cautious of senders who pressure you to open the attachment. Just be careful of email attachments and ensure they are safe before opening them. We need also caution you to stop using non-legitimate web pages for your downloads. If you wish to have secure, file-encoding malicious software-free software, download everything from trustworthy pages.
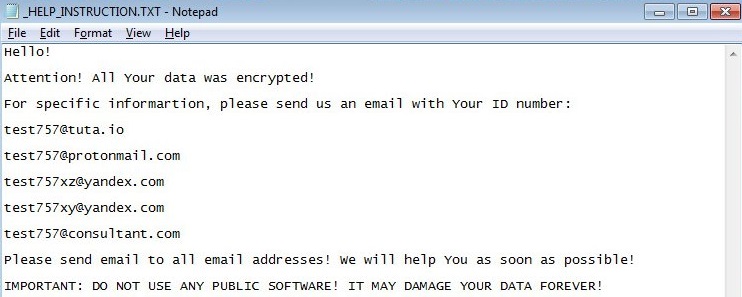
Promptly upon entry, the ransomware will start encoding your data. Your images, documents and other data will no longer be openable. After encoding, you ought to be able to locate a ransom note, if it doesn’t launch on automatically, it should be located in folders with the encoded files. Criminals will state that payment will be required in order to recover your data. Users, however, seem to forget who they are doing business with and do not realize that relying on crooks to stick to their word is somewhat risky. Thus, paying could not bring the desired outcomes. Keep in mind that even after payment, you might not get the decoding utility. Do not believe that just taking your money and not giving you anything in exchange is beneath them. If backup is something you have, you may just abolish Test ransomware and then recover the data. Instead of paying, buy credible backup and terminate Test ransomware.
How to delete Test ransomware
We always caution inexperienced users that the only secure method to erase Test ransomware is by using anti-malware software. Manual Test ransomware elimination is very complex and if you do not know what you are doing, you may you may bring additional damage to your PC. It needs be noted that if you terminate Test ransomware, the security program won’t be able to recover your files
Download Removal Toolto remove Test ransomware
Learn how to remove Test ransomware from your computer
- Step 1. Remove Test ransomware using Safe Mode with Networking.
- Step 2. Remove Test ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Test ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Test ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Test ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

