Is this a severe infection
Nemty 2.6 ransomware file-encoding malicious software, generally known as ransomware, will encode your data. Ransomware is classified to be a very severe threat as you could end up permanently encrypted files. What’s more, contamination happens very easily, therefore making ransomware one of the most damaging malicious program threats. Infection may occur via means such as spam email attachments, malicious adverts or bogus downloads. After contamination, the encryption process will begin, and once it is finished, crooks will demand that you pay a ransom for file decryption. Between $100 and $1000 is probably what will be demanded of you. Whatever you’re requested to pay by this infection, consider every likely consequence before you do. Considering crooks are not compelled to help you in data recovery, what’s preventing them from taking your money and not giving anything in exchange. There are many accounts of users getting nothing after giving into with the requests. This type of thing may reoccur or something may happen to your machine, so it would be wiser to invest the money into some kind of backup. From USBs to cloud storage, you have many options, you just have to choose the correct one. If backup is available, restoring data won’t be a problem. These threats are lurking everywhere, so you need to be prepared. If you want to remain safe, you have to familiarize yourself with likely contaminations and how to guard your system from them.
Download Removal Toolto remove Nemty 2.6 ransomware
Ransomware spread ways
Normally, ransomware uses pretty basic methods to distribute, such as via suspicious downloads, malicious adverts and corrupted email attachments. That doesn’t mean authors won’t use methods that need more ability.
You likely got the infection via email attachment, which might have came from an email that seems entirely real in the beginning. Crooks attach an infected file to an email, which gets sent to many people. Since those emails commonly use sensitive topics, such as money, plenty of users open them without even considering the results. In addition to mistakes in grammar, if the sender, who certainly knows your name, uses Dear User/Customer/Member and firmly encourages you to open the attachment, you should be vary. To explain, if someone whose attachment you ought to open sends you an email, they would would know your name and would not use general greetings, and you would not have to search for the email in spam. Known company names like Amazon are commonly used because users know them, thus are more likely to open the emails. Or maybe you engaged with an infected advert when on a dubious website, or downloaded something from a questionable source. If you were visiting a questionable or compromised website and clicked on an infected advertisement, it might have triggered the file encrypting malware to download. And stick to official sites when it comes to downloads. Bear in mind that you ought to never download programs, updates, or anything really, from pop-up or any other types of adverts. If a program was needed to be updated, it would alert you through the application itself, and not via your browser, and generally they update themselves anyway.
What does it do?
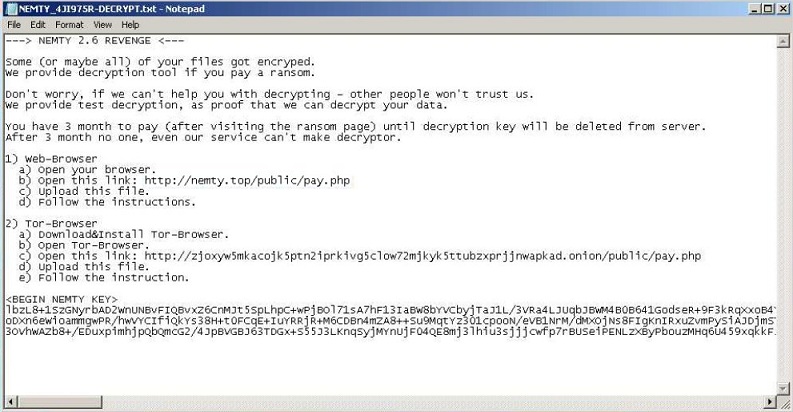
It is possible for ransomware to permanently encode files, which is why it’s such a harmful infection to have. And the encoding process is very quick, it’s only a matter of minutes, if not seconds, for all files you believe are important to become encrypted. Strange file extensions will appear attached to all affected files, from which you may judge which file encrypting malware you’re dealing with. Strong encryption algorithms are used by data encrypting malicious programs to make files inaccessible. You should then see a ransom note, which should explain the situation. The ransom note will have information about how to buy the decryption utility, but think about everything carefully before you opt to comply with the requests. The hackers could simply take your money, they will not feel any obligation to help you. You would also support the cyber criminals’s future malicious software projects, in addition to potentially losing your money. These kinds of threats are thought to have made $1 billion in 2016, and such a successful business will just attract more and more people. As we have said before, a wiser purchase would be backup, which would keep copies of your files safe for when you lose the originals. Situations where your files are put in danger could happen all the time, and you would not need to worry about data loss if you had backup. Terminate Nemty 2.6 ransomware if it’s still present on your device, instead of complying with the demands. These kinds infections can be avoided, if you know how they are spread, so try to familiarize with its spread ways, in detail.
How to uninstall Nemty 2.6 ransomware
You are highly suggested to get anti-malware program to make sure the threat is entirely terminated. Unless you know exactly what you are doing, which might not be the case if you are reading this, we don’t advise proceeding to terminate Nemty 2.6 ransomware manually. If you implement dependable removal software, everything would be done for you, and you would not accidentally end up doing more harm. If the file encrypting malware is still present on your device, the security utility ought to be able to erase Nemty 2.6 ransomware, as those tools are created with the purpose of taking care of such infections. So that you are not left on your own, guidelines below this report have been placed to help you. However unfortunate it may be, those tools are not capable of recovering your files, they’ll just terminate the infection. However, free decryption tools are released by malware specialists, if the ransomware is decryptable.
Download Removal Toolto remove Nemty 2.6 ransomware
Learn how to remove Nemty 2.6 ransomware from your computer
- Step 1. Remove Nemty 2.6 ransomware using Safe Mode with Networking.
- Step 2. Remove Nemty 2.6 ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Nemty 2.6 ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Nemty 2.6 ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Nemty 2.6 ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

