What is ransomware
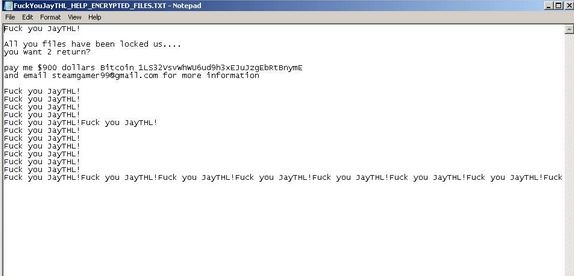
JayTHL ransomware file encrypting malware will lock your files and they’ll be unopenable. In short, it is referred to as ransomware. You may have contaminated your computer in a few ways, possibly either through spam email attachments, infected adverts and downloads. We’ll examine this further in the proceeding section. Handling a file-encrypting malware infection could have serious consequences, therefore it is crucial that you’re informed about its spread methods. If that isn’t an infection you are familiar with, seeing locked files can be especially surprising. When the encoding process is finished, you’ll notice a ransom note, which will explain that you must pay a certain amount of money to get a decryption tool. Do not forget who you’re dealing with if you consider paying the ransom, because it is dubious cyber crooks will take the trouble sending a decryption software. It’s more possible that you’ll be ignored after you pay. You’d also be supporting an industry that does millions of dollars in damages yearly. We encourage looking into a free decryptor, maybe a malware researcher was able to crack the ransomware and create a decryption tool. Research a free decryptor before you even think about giving into the requests. For those with backup available, simply terminate JayTHL ransomware and then recover data from backup.
Download Removal Toolto remove JayTHL ransomware
How does ransomware spread
You might have gotten the infection in a couple of ways, which will be discussed in a more detailed manner. Ransomware typically sticks to basic methods, but that’s not to say that more sophisticated ones aren’t employed at all. Spam email and malicious downloads are popular among low-level ransomware creators/distributors as not much skill is needed to implement them. It’s probable that your machine got contaminated when you opened an email attachment that was infected. Criminals attach an infected file to a somewhat authentic appearing email, and send it to future victims, whose email addresses they probably acquired from other crooks. Generally, those emails have hints of being bogus, but for those who have never encountered them before, it might seem quite convincing. You can notice particular signs that an email may be harboring ransomware, such as grammar mistakes in the text, or the sender’s email address being weirdly random. You might also encounter the sender feigning to be from a legitimate company because that would cause people to lower their guard. It’s better to be safe than sorry, thus, always check the sender’s email address, even if you’re familiar with them. If your name isn’t mentioned in the email, for example, in the greeting, that ought to raise suspicion. If a company with whom you’ve dealt with before emails you, they will always address you by name, instead of Member/User/Customer. If you’re an Amazon customer, your name will be inserted in the greeting in every email they send you, because it is done automatically.
To summarize, look into the sender and ensure they are who they say they are before you rush to open the attachment. You need to also be cautious and not press on adverts when on pages with a questionable reputation. By just clicking on a malicious ad you might be allowing ransomware to download. It does not matter what the ad could be offering, just don’t press on it. Your device may also become contaminated if you download from sources that aren’t trustworthy, such as Torrents. Downloads via torrents and such, may be harmful, thus at least read the comments to ensure that what you’re downloading is not malicious. Vulnerabilities in software may also be used for malicious software infection. That is why updating your programs is so important. Software vendors frequently release patches for vulnerabilities, all you have to do is install them.
How does ransomware act
As soon as you open the infected file, the will scan your system and encode certain files. Expect to see documents, photos and videos to be encrypted because those files are very likely to be valuable to you. Once the files are discovered, they’ll be encrypted with a powerful encryption algorithm. If you aren’t sure which files have been affected, check the file extensions, if you notice unknown ones, they have been affected. If you are still unsure about what happened, a ransom note will explain the situation and request that you pay a certain amount of money to get a decryptor. The sum asked is different, depending on the ransomware, but will be somewhere between $50 and $1000, to be paid in digital currency. We’ve already explained why paying isn’t the suggested choice, but in the end, the decision is yours. Do not forget to also consider other file recovery options. If the ransomware was crackable, it is likely malware analysts were able to make a free decryption utility. Try to remember if you have backed up at least some of your files somewhere. It might also be possible that the Shadow copies of your files were not deleted, which means they’re recoverable through Shadow Explorer. And ensure you buy backup so that data loss is not a possibility. If you had taken the time to backup your files, they should be recovered after you erase JayTHL ransomware.
JayTHL ransomware termination
Unless you are absolutely certain about what you are doing, we don’t suggest you attempt manual elimination. Your device might sustain irreversible damage if you make a mistake. It would be much safer to employ a malicious software removal tool instead. You shouldn’t encounter trouble as those programs are created to erase JayTHL ransomware and similar infections. As this utility will not help you decrypt the data, don’t expect to find your files recovered after the infection has been eliminated. File restoring will be yours to carry out.
Download Removal Toolto remove JayTHL ransomware
Learn how to remove JayTHL ransomware from your computer
- Step 1. Remove JayTHL ransomware using Safe Mode with Networking.
- Step 2. Remove JayTHL ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove JayTHL ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove JayTHL ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove JayTHL ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

