About IGAL ransomware
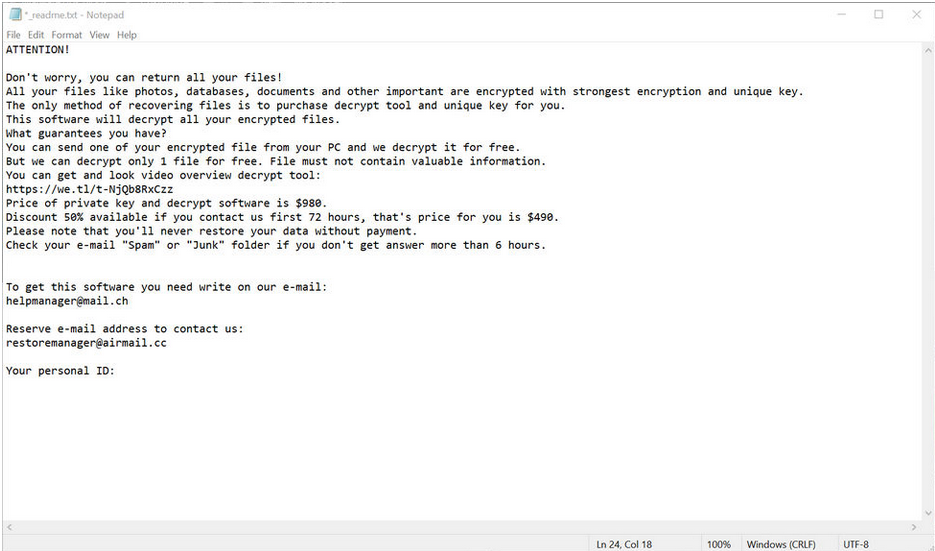
IGAL ransomware will encrypt your files, and that’s why infection is something you have to bypass. Ransomware is the classification you will will be more acquainted with, however. There’s a high likelihood that you recently opened an infected attachment or downloaded from harmful sources, and that’s how the infection got in. We’ll explain these methods in more details and provide tips on how you may bypass similar infections in the future. A file-encrypting malware infection could lead to very severe consequences, so you must be aware of its distribution ways. If that isn’t an infection you’re familiar with, seeing that your data has been encrypted might be particularly shocking. When the encryption process is finished, you will notice a ransom message, which will explain that a payment is needed to get a decryption program. If you consider paying to be a good idea, we’d like to remind you that you are dealing with crooks, and they’re unlikely to aid you, even if you pay. It’s much more probable that you will not get a decryptor. You should also consider where the money would be going, it will probably support other malware. We encourage looking into a free decryptor, maybe a malware analyst was able to crack the ransomware and thus create a decryptor. At least try to find a decryptor before you give into the requests. If backup was made prior to the ransomware infection, after you remove IGAL ransomware there you shouldn’t have issues when it comes to restoring data.
Download Removal Toolto remove IGAL ransomware
IGAL ransomware distribution ways
Your computer might have become infected in a couple of ways, which will be discussed in more detail. Ransomware tends to employ quite simple ways for infection but a more sophisticated method isn’t impossible. Ransomware creators/distributors with little knowledge/experience tend to stick to methods that don’t need advanced knowledge, like sending the infection added to emails or hosting the infection on download platforms. It is quite probable that spam email is how you got the malware. A contaminated file is added to a somewhat convincingly written email, and sent to possible victims, whose email addresses crooks possibly acquired from other cyber criminals. Generally, the email wouldn’t seem convincing to those who are experienced in these matters, but if you’ve never ran into it before, you opening it wouldn’t be that surprising. If you see that the sender’s email address is completely random, or if the text is full of grammar mistakes, that may be a sign that it’s an email harboring malware, particularly if it landed in your spam folder. Users tend to drop their guard if they are familiar with the sender, so you might encounter hackers pretending to be from some famous company like eBay. You may never be too cautious, thus, always check if the email matches the sender’s legitimate one. You ought to also look for your name not used in the beginning. Senders whose attachments are crucial enough to be opened ought to know your name, therefore common greetings like Sir/Madam, User or Customer would not be used. To be more specific, if you are an Amazon customer, your name will be automatically inserted into any email you are sent.
To summarize, look into the sender and ensure they are who they say they are before you rush to open the attachment. You ought to also be cautious and not press on advertisements when on pages with a questionable reputation. Not all adverts are safe to press on, and you might be redirected to a site that’ll launch a dangerous download. The ads you see on those web pages are certainly not trustworthy, they’ll only bring trouble. Don’t download from sources that aren’t reliable because you might easily get malware from there. Downloading via torrents and such, are a risk, thus at least read the comments to ensure that you are downloading safe content. In other cases, software flaws may be used by the ransomware to get in. And that is why it is so important that you update your programs. Patches are released regularly by vendors, all you have to do is install them.
What happened to your files
The encryption process will begin as soon as you. It targets documents, photos, videos, etc, all files that might hold some importance to you. The file-encrypting malware will use a strong encryption algorithm to lock files as soon as they are discovered. A strange file extension added will help you figure out with files have been affected. You’ll soon come across a ransom message, which will explain how you might restore your files, aka how much you need to pay for a decryption utility. How much the decryption program costs varies from ransomware to ransomware, you might be demanded $20 or a $1000. It is your choice to make whether to pay the ransom, but do consider why this option isn’t encouraged. Don’t forget to also think about other data recovery options. Malware researchers are sometimes successful in cracking ransomware, therefore you may find a free decryption utility. Or maybe you have backed up the files some time ago but simply do not recall doing so. It could also be possible that the Shadow copies of your files weren’t erased, which means you might restore them through Shadow Explorer. If you have not done it yet, we hope you invest in some kind of backup soon, so that you do not endanger your files again. If backup is available, you may proceed to recover files from there after you fully remove IGAL ransomware.
IGAL ransomware elimination
It ought to be said that it isn’t encouraged to try manual termination. If you make a mistake, your computer may suffer permanent damage. It would be best for you to get anti-malware, a tool that will take care of the infection for you. The utility ought to successfully eliminate IGAL ransomware since it was created for this intent. Bear in mind, however, that the software isn’t capable of recovering your files, so they will remain the same after the infection is gone. You’ll need to carry out data restoring yourself.
Download Removal Toolto remove IGAL ransomware
Learn how to remove IGAL ransomware from your computer
- Step 1. Remove IGAL ransomware using Safe Mode with Networking.
- Step 2. Remove IGAL ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove IGAL ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove IGAL ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove IGAL ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

