What can be said about file-encrypting malware
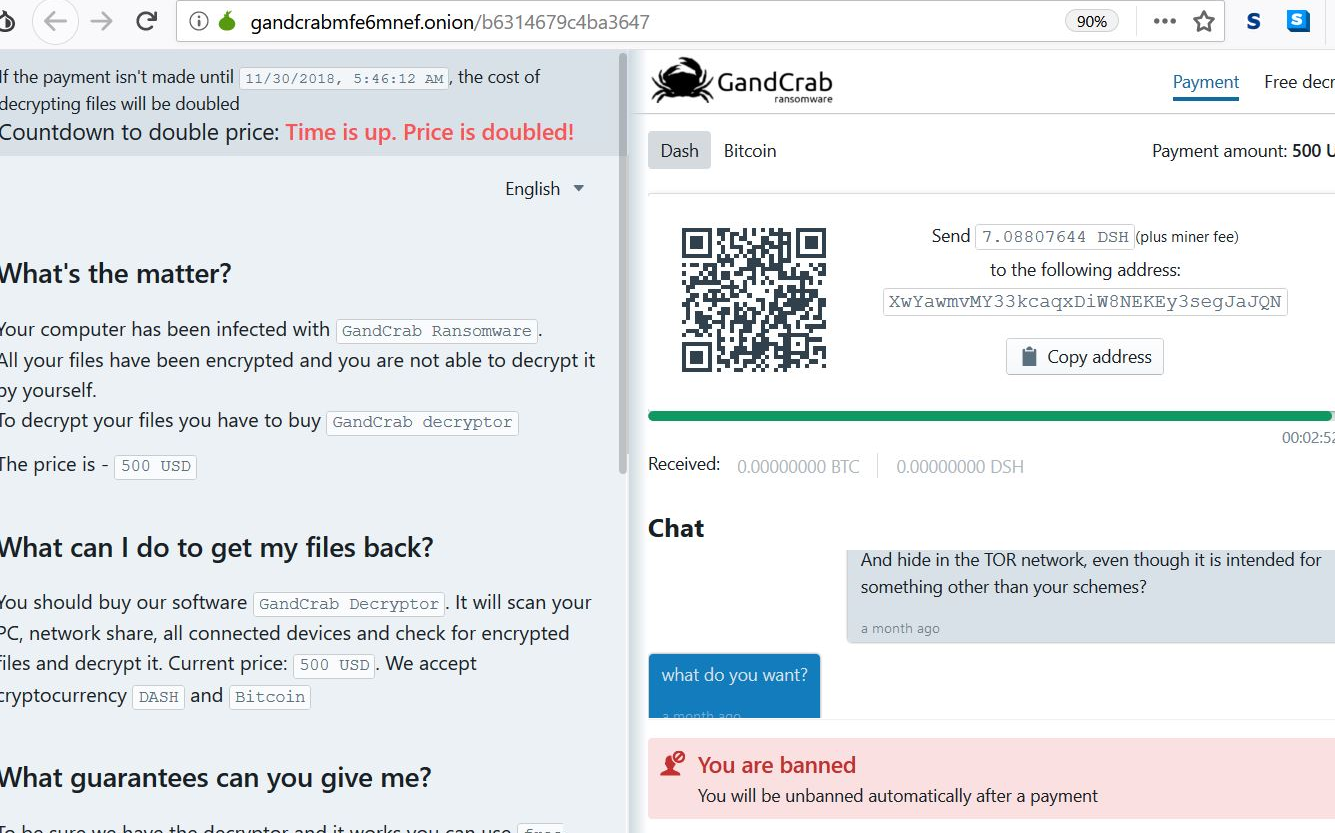
Gandcrab 5.1 is is a file-encrypting kind of malware. Malicious downloads and spam emails are most commonly used to spread the ransomware. Ransomware will lock your files immediately upon infection and ask for money, which is why we consider it to be a highly harmful threat. If ransomware researchers manage to crack the file-encrypting malicious software, they could create a free decryption tool, or if you have backup, file loss would not be a problem. You not having backup can lead to file loss as file recovery using other methods is not always likely. Some may feel paying the ransom is the solution, but we ought to caution you that it doesn’t guarantee data recovery. Cyber criminals already encrypted your files, what’s preventing them from becoming even more horrible by not decoding your files after payment. Since payment is not a reliable file recovery choice, you should simply eliminate Gandcrab 5.1.
Download Removal Toolto remove Gandcrab 5.1
Malicious files infecting with GANDCRAB 5.1 Ransomware:
SHA-256:85671f4675ccc98133a5a6de2e4faeb6df119ad9460f3651e231eaba4ce2b872
File name:3449440902.exe
File size:185.5 KB
SHA-256:c1a66da25419855f684261ac55f796127d84ca7bb9e089b1eb18afde66d1da7c
File name:GandCrab v5.1.exe
File size:421 KB
SHA-256:07de185bb18610f471a31358c74c2e2da0dc505ade21cbe9cae5c8ba3fd66add
File name:putty.exe
File size:595 KB
SHA-256:47b9249590b764e24d0da606efa1858d41bdd57886329014b61f44701668c080
File name:Analysis’s Restrain
File size:630 KB
SHA-256:befb77f972b225791b9f84644939be3e599f0bc361b7a20ad4cde696361c78ba
File name:Technologyword
File size:694.5 KB
SHA-256:5b13e0c41b955fdc7929e324357cd0583b7d92c8c2aedaf7930ff58ad3a00aed
File name:output.115120150.txt
File size:609 KB
SHA256:c7197601b0e5cf5a38abe626007ffd05d36d4f205b6b62ab5d6f940590d42c8d
File name: 4.exe
SHA-256:9e90a004a26fe2f58f4c725a7034fa6c4fd95000dc86c573e2036a75e83c0705
File name:1.exe
File size:288.5 KB
The primary infection method that was used so far in relation to GANDCRAB 5.1 infection is e-mails that are composed in the following way:
From: Deanna Bennett <>
Subject: Payment Invoice #93611
Attachment: DOC402942349491-PDF.7Z
Dear Customer,
To read your document please open the attachment and reply as soon as possible.
Kind regards,
TCR Customer Support
Besides the “Payment Invoice #93611” subjects above, we have also detected other fake subject e-mails:
- Document #72170
- Invoice #21613
- Order #87884
- Payment #72985
- Ticket #07009
- Your Document #78391
- Your Order #16323
- Your Ticket #23428
How does the file-encrypting malware affect the device
The most possible way you got the file-encoding malicious software was via spam email. All malware authors have to do is attach an infected file to an email and send it to innocent users. When a user opens the email attachment, the ransomware downloads onto the device. This is why opening every single email attachment that lands in your inbox is not exactly smart. You can usually differentiate a malicious email from a secure one pretty easily, you merely need to learn the signs. Be specially cautious of senders pressing you into opening the attachment. In general, be careful because any email attachment that lands in your inbox could contain ransomware. Another way to authorize the file-encoding malicious software to contaminate is by downloading from not reliable web pages, which could be compromised without difficulty. If you want safe, ransomware-free software, only download from credible portals.
Shortly upon infection, the ransomware will start encrypting your data. Your images, documents and other files will no longer be openable. You will then notice a ransom note, which will clarify what has happened. Cyber crooks will state that payment will be needed so as to recover your data. Criminals’ behavior is unpredictable therefore doing business with them may become quite difficult. So by giving into the demands, you’re risking losing your money. You receiving the decoding tool for which you have to pay, may not necessarily happen. There is a chance that by paying you will lose your money and not get back your data. Having backup may have saved you a lot of issues, if you had it prior to encryption, you could just uninstall Gandcrab 5.1 and recover data from there. Whether you have backup or not, we encourage you abolish Gandcrab 5.1.
Gandcrab 5.1 removal
You are encouraged to get anti-malware software and have it remove Gandcrab 5.1 for you. By hand Gandcrab 5.1 removal is quite difficult so if you’re inexperienced, you may end up damaging your OS further. It ought to be said that if you abolish Gandcrab 5.1, the security software won’t be able to restore your data
Download Removal Toolto remove Gandcrab 5.1
Learn how to remove Gandcrab 5.1 from your computer
- Step 1. Remove Gandcrab 5.1 using Safe Mode with Networking.
- Step 2. Remove Gandcrab 5.1 using System Restore
- Step 3. Recover your data
Step 1. Remove Gandcrab 5.1 using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Gandcrab 5.1.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Gandcrab 5.1 using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

