What is ransomware
ATKL ransomware malware is considered to be highly harmful because of its intention to lock your data. Ransomware is the more known name of this kind of malware. If you’re unsure about how your device got contaminated, you probably opened a spam email attachment, clicked on an infected advertisement or downloaded something from a source you should have bypassed. If you’re looking for tips on how the infection might be avoided, continue reading this article. Ransomware isn’t thought to be so harmful for nothing, if you wish to avoid likely severe outcomes, be careful to prevent its infection. It can be especially shocking to find your files encrypted if it’s your first time hearing about ransomware, and you have no idea what type of infection it is. A ransom message should make an appearance soon after the files are locked, and it will explain that a payment is needed to decrypt your data. Do keep in mind that you’re dealing with crooks and they’re unlikely to feel any accountability to aid you. You are more likely to be ignored after you make the payment than receive a decryptor. We’d also like to point out that your money will probably support future malware projects. It ought to be mentioned that malware specialists do help victims of ransomware to restore files, so you may be in luck. Look into that before paying even crosses your mind. For those with backup available, you simply need to eliminate ATKL ransomware and then recover files from backup.
Download Removal Toolto remove ATKL ransomware
How is ransomware spread
This section will talk about how your machine got infected and whether the threat may be prevented in the future. It mainly employs quite simple ways for infection but more elaborated ones aren’t out of the question. Spam email and malware downloads are popular among low-level ransomware creators/distributors as not much skill is required to employ them. Spreading the ransomware via spam is still possibly the most common infection method. An infected file is attached to a kind of authentic email, and sent to all possible victims, whose email addresses they store in their database. Generally, the email wouldn’t convince users who have encountered spam before, but if you have never come across it before, you opening it wouldn’t be that unexpected. There might be signs that you are dealing with malware, something like a nonsensical email addresses and a lot of grammar mistakes in the text. It wouldn’t be shocking if you encountered popular company names like Amazon or eBay because people would drop their guard when dealing with a sender they know. It is recommended that even if you know the sender, the sender’s address should still be checked. A red flag should also be the greeting not having your name, or anywhere else in the email for that matter. Senders who say to have some kind of business with you ought to be familiar with your name, therefore basic greetings like Sir/Madam, User or Customer wouldn’t be used. For example, Amazon automatically inserts the names customers have provided them with into emails they send, therefore if the sender is actually Amazon, you will find your name.
In a nutshell, before hurrying to open email attachments, make sure the sender is who they insist they are and the attached file will not cause a disaster. Also, don’t interact with ads when on questionable web pages. If you press on a malicious advertisement, malware might download. Whatever the advert could be endorsing, try not to click on it. Using unreliable pages as download sources could also bring about a contamination. If you are doing downloads via torrents, the least you could do is read the comments before you proceed to download something. Software flaws could also be used for malware infection. Which is why it is so crucial that you update your software. All you need to do is install the updates, which software vendors release when the vulnerability becomes known.
What does it do
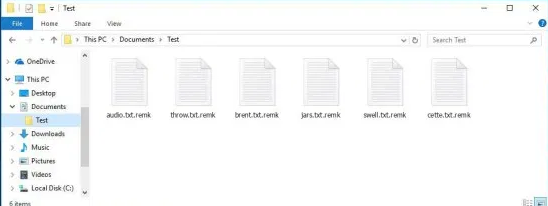
Ransomware generally begin the encoding process as soon as you launch it. As it has to hold some leverage over you, all your valuable files, like media files, will become targets. So as to encrypt the located files, the file-encrypting malware will use a powerful encryption algorithm to lock your data. You will see that the files that were affected have an unknown file extension added to them, which will help you identify encrypted files promptly. A ransom message should then pop up, which will propose you a decryptor in exchange for money. Ransomware ask for different sums, you may be demanded to pay $100 or a even up to $1000. It is your decision to make whether you want to pay the ransom, but do think about why ransomware investigators do not suggest that option. Researching other options to restore data would also be a good idea. Maybe a decryptor has been created by people specializing in malware research. Maybe a backup is available and you simply don’t remember it. You should also try file restoring via Shadow Explorer, the ransomware might have not erased the Shadow copies of your files. If you are yet to do it, we hope you buy some kind of backup soon, so that you don’t jeopardize your files again. However, if you had backed up files prior to the infection taking place, file recover ought to be carried out after you uninstall ATKL ransomware.
Ways to delete ATKL ransomware
The manual termination option is not recommended, for one big reason. If something goes incorrectly, permanent damage could be brought about to your system. It would be safer to use an anti-malware tool because it would erase the threat for you. Those programs are made with the purpose to remove ATKL ransomware and similar infections, thus there should not be issue. Because this program won’t aid you in decrypting data, do not expect to find restored files after the infection has been terminated. You will need to carry out data restoring yourself.
Download Removal Toolto remove ATKL ransomware
Learn how to remove ATKL ransomware from your computer
- Step 1. Remove ATKL ransomware using Safe Mode with Networking.
- Step 2. Remove ATKL ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove ATKL ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove ATKL ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove ATKL ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

