Why are your files encrypted
Honor ransomware will encode your files the minute it invades your machine since it’s malevolent file-encrypting software. Ransomware is a very alarming infection because it will encode your files and demand money in exchange for a decoding way. Unfortunately, usually, users are left with unusable files. You most likely opened a dangerous email attachment or fell for a deceiving download recently and that is how you got corrupted. This is why professionals have been alerting users for a very long time about the dangers of being careless on the Internet. Victims are demanded to pay a ransom when they are contaminated and that is the last thing they should do for various reasons. Crooks could just take your money and leave your files as they are, locked. Instead of giving into the demands, you ought to erase Honor ransomware.
Download Removal Toolto remove Honor ransomware
Ransomware distribution ways
The major The primary ways aggressive file-encoding software is distributed are spam email attachments and fake downloads. Never open email attachments from senders you aren’t familiar with, even if you are curious, without firstly guaranteeing that they won’t bring about damage. If you aren’t vigilant, ultimately, you may end up with file-encrypting malware. Ransomware can also be spread via programs downloads, so be wary about where you obtain your programs from. If you want to guarantee that you download from safe sources only trust legitimate/official sites. If you believe you will get secure downloads from sources, you are in for a surprise. If you have a tendency of obtaining questionable programs, your chance of getting infiltrated with ransomware is that much higher.
How does ransomware affect the device?
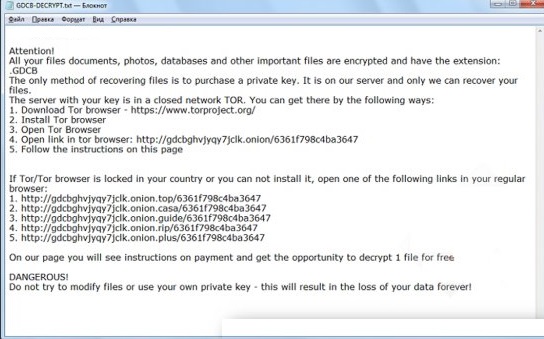
A ransomware infection is thought to be rather serious as it will lock your files. Decoding tools are sometimes presented by malware specialists nevertheless it’s not always possible. File loss could be what you will have to deal with. The first thing the file-encrypting malware will do upon entering is implement complex encryption algorithms to encrypt your data. After that is done, a ransom note a notification with info about data recovery will appear. No matter what the amount is, If you’re considering paying, reconsider your decision. There are no promises that you could get your data back, even if you pay as the crooks can just take your money. You would also be basically backing their future projects.Backup may have been the easiest solution to this problem. You should invest the money demanded by the ransomware into dependable backup so that you are not put in this situation again. Whether you have copies of files saved somewhere else or not, you still ought to delete Honor ransomware.
Honor ransomware elimination methods
Honor ransomware elimination could be too hard if you carried it out yourself. Which is why we would encourage you get malware removal program to remove Honor ransomware. However, while it would delete Honor ransomware it is not capable of decrypting your data.
Download Removal Toolto remove Honor ransomware
Learn how to remove Honor ransomware from your computer
- Step 1. Remove Honor ransomware using Safe Mode with Networking.
- Step 2. Remove Honor ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Honor ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Honor ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Honor ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

