What can be said about file-encoding malicious software
Uridzu ransomware might be the ransomware responsible for your file encryption. Dangerous downloads and spam emails are generally used to spread the file-encoding malicious software. Ransomware is believed to be one of the most damaging malware you could get because it encrypts data, and asks that you pay to get them back. If if you routinely backup your files, or if damaging program specialists create a free decryptor, file-recovery would not be hard. Other than that, it might not be possible to recover your files. Paying the ransom does not mean you will get your files back so bear that in mind if you’re thinking about paying. You are dealing with crooks who might not feel obliged to help you with anything. We would advise that you terminate Uridzu ransomware instead of giving into the requests.
Download Removal Toolto remove Uridzu ransomware
How does ransomware behave
If you recently opened an email attachment it is likely you obtained the infection from there. Malware authors adjoin infected files to an email and send it to to hundreds or even thousands of users. As soon as you open the email attachment, the file-encoding malicious software will download onto the OS. If you open all emails and attachments you receive, you might be putting your operating system at risk. You ought to be able to differentiate a malicious email from a secure one without difficulty, you just need to learn the signs. You being urged by the sender into opening the attachment is a big red flag. You are suggested to always ensure the attachments are secure before you open them if you want to avoid malevolent software. Downloading from unsecure web pages may also lead to ransomware. Only trust official websites with safe, file-encoding malware-free software.
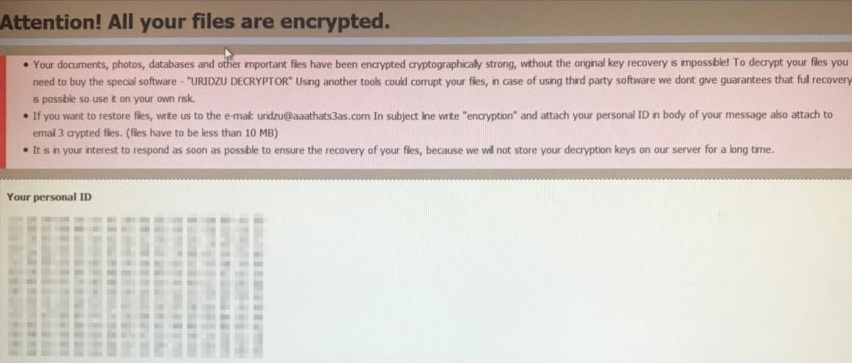
The encryption procedure will be finished before you even understand what is going on. The major targets of the contamination will be images, documents and videos. After the encryption procedure is complete, you ought to be able to find a ransom note, if it does not launch on its own, it should be placed in all folders that contain the encrypted data. In exchange for data recovery, you are asked for money. When dealing with criminals, there are no reassurances about how they will act. This is why paying isn’t suggested. There are no promises that you will be sent a decoding key if you pay. There is nothing preventing cyber criminals from just taking your money, and leaving your files encrypted. Had you had backup, you might just remove Uridzu ransomware and then recover the files. If you do not have backup, it would be smarter to invest the ransom sum into trustworthy backup after you abolish Uridzu ransomware.
How to remove Uridzu ransomware
Anti-malware is needed in order to erase Uridzu ransomware. By hand Uridzu ransomware uninstallation is very complex and if you don’t know what you are doing, you might end up damaging your machine further. Anti-malware software is made to abolish Uridzu ransomware and similar contaminations, so don’t expect it to recover your data
Download Removal Toolto remove Uridzu ransomware
Learn how to remove Uridzu ransomware from your computer
- Step 1. Remove Uridzu ransomware using Safe Mode with Networking.
- Step 2. Remove Uridzu ransomware using System Restore
- Step 3. Recover your data
Step 1. Remove Uridzu ransomware using Safe Mode with Networking.
a) Step 1. Access Safe Mode with Networking.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Choose Safe Mode with Networking

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Networking.

b) Step 2. Remove Uridzu ransomware.
You will now need to open your browser and download some kind of anti-malware software. Choose a trustworthy one, install it and have it scan your computer for malicious threats. When the ransomware is found, remove it. If, for some reason, you can't access Safe Mode with Networking, go with another option.Step 2. Remove Uridzu ransomware using System Restore
a) Step 1. Access Safe Mode with Command Prompt.
For Windows 7/Vista/XP
- Start → Shutdown → Restart → OK.

- Press and keep pressing F8 until Advanced Boot Options appears.
- Select Safe Mode with Command Prompt.

For Windows 8/10 users
- Press the power button that appears at the Windows login screen. Press and hold Shift. Click Restart.

- Troubleshoot → Advanced options → Startup Settings → Restart.

- Choose Enable Safe Mode with Command Prompt.

b) Step 2. Restore files and settings.
- You will need to type in cd restore in the window that appears. Press Enter.
- Type in rstrui.exe and again, press Enter.

- A window will pop-up and you should press Next. Choose a restore point and press Next again.

- Press Yes.
Step 3. Recover your data
While backup is essential, there is still quite a few users who do not have it. If you are one of them, you can try the below provided methods and you just might be able to recover files.a) Using Data Recovery Pro to recover encrypted files.
- Download Data Recovery Pro, preferably from a trustworthy website.
- Scan your device for recoverable files.

- Recover them.
b) Restore files through Windows Previous Versions
If you had System Restore enabled, you can recover files through Windows Previous Versions.- Find a file you want to recover.
- Right-click on it.
- Select Properties and then Previous versions.

- Pick the version of the file you want to recover and press Restore.
c) Using Shadow Explorer to recover files
If you are lucky, the ransomware did not delete your shadow copies. They are made by your system automatically for when system crashes.- Go to the official website (shadowexplorer.com) and acquire the Shadow Explorer application.
- Set up and open it.
- Press on the drop down menu and pick the disk you want.

- If folders are recoverable, they will appear there. Press on the folder and then Export.
* SpyHunter scanner, published on this site, is intended to be used only as a detection tool. More info on SpyHunter. To use the removal functionality, you will need to purchase the full version of SpyHunter. If you wish to uninstall SpyHunter, click here.

